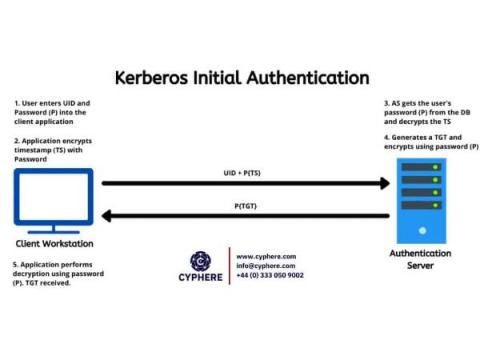
Kerberos Authentication: Basics to Kerberos attacks
Developed by MIT, Kerberos Authentication Protocol is the default authentication service for Microsoft Active Directory. It is named after the three-headed dog (Cerberus) found in Greek mythology, because the security protocol involves three major steps in the entire authentication process. Although Kerberos is a technology used by Microsoft Windows, by default, its implementations in other operating systems, such as Linux, FreeBSD and macOS, are also present.