Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Containers
Container Security Fundamentals - Containers Are Just Processes
Encryption in container environments
Kubernetes has become the de facto standard for container orchestration, providing a powerful platform for deploying and managing containerized applications at scale. As more organizations adopt Kubernetes for their production workloads, ensuring the security and privacy of data in transit has become increasingly critical.
Who's Who in Cloud Security? CSPM, CIEM, CWPP & CNAPP Explained
Cloud Native Application Protection Platforms – or CNAPP solutions – are steadily gaining traction as the best solutions to address Cloud Native security. Regardless of your cloud adoption maturity (whether you’re PoC-ing some services in the cloud, running a few applications, or fully embracing this new era), We’re sure you have likely already noticed that cloud-native security is different from IT-managed data center security. But how exactly is it different?
How doNotTrack policies work in the Calico eBPF dataplane
Almost all modern network systems, including stateful firewalls, make use of connection tracking (“conntrack”) because it consumes less processing power per packet and simplifies operations. However, there are use cases where connection tracking has a negative impact, as we described in Linux Conntrack: Why it breaks down and avoiding the problem.
Case study: Calico on AWS enables turnkey networking and security for Rafay's enterprise-grade Kubernetes Operations Platform
Organizations are adopting Kubernetes on Amazon Web Services (AWS) to modernize their applications. But Kubernetes clusters and application lifecycles demand a considerable investment of cost and resources, especially for edge applications.
Sysdig Training series - Introduction to Sysdig Secure
How Namespace-as-a-Service Enables Self-Service Kubernetes Recovery
Kubernetes has become the de facto standard for container orchestration and management, providing a powerful platform for deploying and managing containerized applications. One of the key benefits of Kubernetes is its support for namespaces, which allow users to isolate groups of resources within a cluster, providing a level of isolation and resource allocation for different applications or teams.
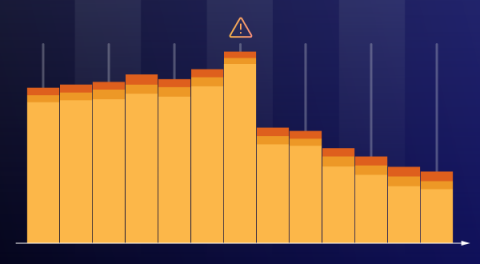
Track Risk Trends in your Container Images with Sysdig Risk-based Vulnerability Management
The number of detected common vulnerabilities and exposures (CVEs) has significantly increased in the past decade. In the last five years, security researchers reported over 100,000 new CVEs. The highest reported annual figure was in 2022, with over 25,000 new CVEs. This number can overwhelm any security team if it’s not managed correctly between assessment, reporting, remediation, and monitoring.