Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
SIEM
The latest News and Information on Security Incident and Event Management.
Elastic SIEM detections
With the release of Elastic Security 7.6, we've announced our creation of a modern detection engine that provides SOC teams with a unified SIEM rule experience through Elastic SIEM detections. The detection engine draws from a purpose-built set of Elasticsearch analytics engines and runs on a new distributed execution platform in Kibana.
ManageEngine named in Gartner's Magic Quadrant for Security Information and Event Management four years running!
The cybersecurity market is ever-changing and primarily driven by sophisticated cyberattacks, disruptive technological growth, and stringent data protection regulations like the GDPR and CCPA. We are constantly evolving our solutions to meet these dynamic market needs. We believe our recognition in the Gartner Magic Quadrant for security information and event management (SIEM) for the fourth consecutive time proves that our efforts have been channeled in the right direction.
Elastic SIEM for home and small business: SIEM overview
Hello, security enthusiasts! This is part seven (can you believe it?) of the Elastic SIEM for home and small business blog series. If you haven’t read the first six blogs in the series, you may want to before going any further. In the prerequisite blogs we created our Elasticsearch Service deployment (part 1), secured access to our cluster by restricting privileges for users and Beats (part 2), then we created an ingest pipeline for GeoIP data and reviewed our Beats configurations (part 3).
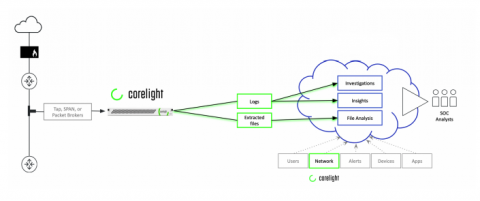
Securing IaaS, PaaS, and SaaS in 2020 with a Cloud SIEM
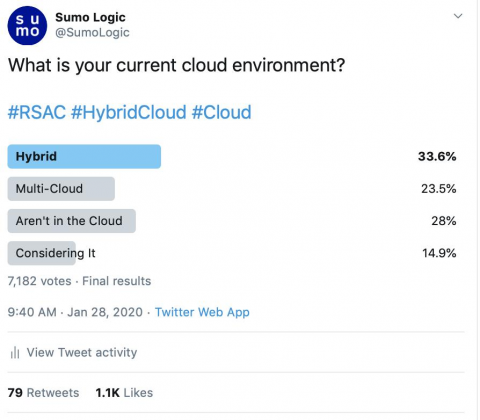
Pre-RSA Twitter Poll: 3 Interesting Observations on SOC, SIEM and Cloud
SIEM Yara Rules
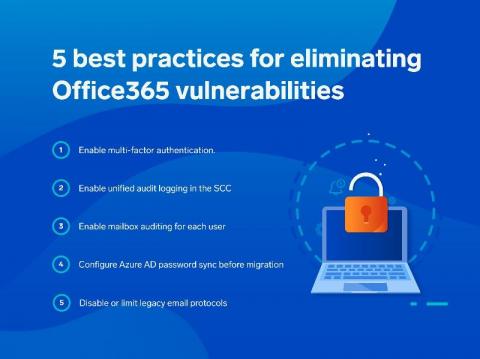
How to Secure Office365 with Cloud SIEM
What is Cyber Security Ontology?
The amount of APTs, ransomware and phishing attacks have been growing steadily for the last few years. As a result, cyber security professionals have been looking for better methods to protect organizations. In this article, we will discuss one of those newly popularized methods: cyber security ontology.
The Vulnerability Management Maturity Model and Its Stages
The need for a mature cybersecurity process in today’s corporate environment is becoming ever more critical. As hackers are becoming more and more sophisticated, so our management and defense systems should also be strengthened accordingly. While there are many components that make up a solid security program within an organization, today, we will shed a light on one essential of these components, which is a vulnerability management maturity model.