Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest Videos
From Zero to DevSecOps: How to Implement Security at the Speed of DevOps
Your organization has already embraced the DevOps methodology? That’s a great start. But what about security? It’s a fact - many organizations fear that adding security to their DevOps practices will severely slow down their development processes. But this doesn’t need to be the case. the DevOps pipeline
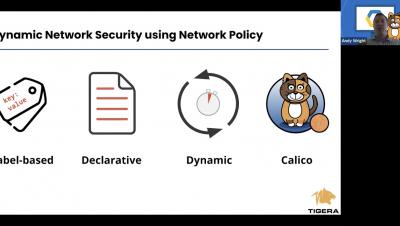
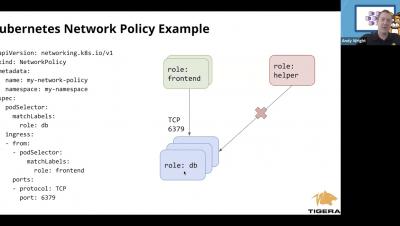
How to Implement Network Policy in Google GKE to Secure Your Cluster
By default, pods are non-isolated; they accept traffic from any source. The Google GKE solution to this security concern is Network Security Policy that lets developers control network access to their services. Google GKE comes configured with Network Security Policy using Project Calico which can be used to secure your clusters. This class will describe a few use cases for network security policy and a live demo implementing each use case.
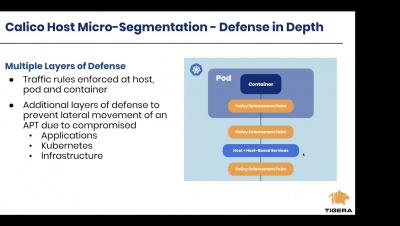
Getting up and running with Calico Host Micro segmentation Protection on AWS
In this online training, we will explain how to install and configure Calico on a vm/host to apply network policy to resources outside your K8s cluster. The talk will be primarily a walkthrough and demo and you will receive all manifests and instructions to do the demo on your own after the session.
Ask the Experts: How to Start Your Career in Cybersecurity
In this video, Tripwire asked industry experts to share their advice for individuals looking to jump-start their career in the field of cybersecurity. What skills are most important? How do you get involved?
How to Implement Network Policy in Amazon EKS to Secure Your Cluster
By default, pods are non-isolated; they accept traffic from any source. The Amazon EKS solution to this security concern is Network Policy that lets developers control network access to their services. Amazon EKS comes configured with Network Policy using Project Calico which can be used to secure your clusters. This class will describe a few use cases for network policy and a live demo implementing each use case.
How to Implement Network Policy in Azure AKS to Secure Your Cluster
By default, pods are non-isolated; they accept traffic from any source. The Azure AKS solution to this security concern is Network Policy that lets developers control network access to their services. The Azure AKS comes configured with Network Policy using Project Calico which can be used to secure your clusters. This class will describe a few use cases for network policy and a live demo implementing each use case.
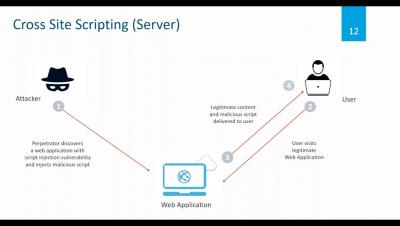
Outpost24 Webinar - You may be in Lock-down but are your applications?
You may be in Lock-down but are your web applications?
Ask the Experts: Is There a Cybersecurity Skills Gap?
In this video, Tripwire asked cybersecurity experts to weigh-in on one of the most widely debated industry issues: the skills gap. Is there a cyber talent shortage? If so, how can organizations and the industry as a whole come together to overcome it?
Security And Compliance for Remote Federal Workers
With much of the federal workforce now using laptops to work from home, how can agencies like yours overcome VPN hurdles and ensure the same standard of security monitoring? Compliance frameworks help you achieve and maintain remote asset security with detailed, step-by-step guidance on best practices, including extending security controls to cover remote laptops and other endpoints employees may be using from home in the wake of Covid-19.