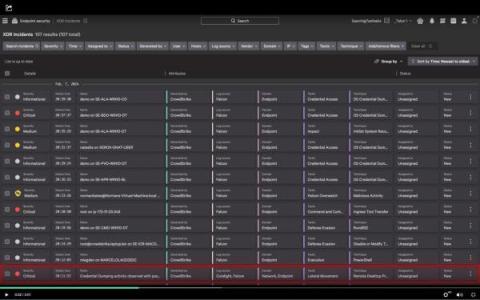
Integrating Snyk Code SAST results in your ServiceNow workflows
Application security teams often lack the crucial information and visibility needed to find, prioritize, and remediate risks in their most business-critical applications. To solve this application security challenge, ServiceNow and Snyk have partnered to provide a singular view of the risk within these applications — exposing the severity and criticality of vulnerabilities while providing actionable workflows to boost your overall security posture.