Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Zero Trust
NIST Zero Trust Architecture Compliance
Netskope Private Access Delivers Full ZTNA Capabilities, Including Top Use Cases
The shift to remote and hybrid work at scale has created unprecedented demand for our cloud-delivered Zero Trust Network Access(ZTNA) solution, Netskope Private Access(NPA). This is no surprise.
Netskope Integrates Targeted RBI Within SASE Architecture
There is the marketing of secure access service edge (SASE), and then there is the actual integration of key capabilities that provide the benefits of less complexity, consolidation, and lower cost of operations a properly implemented SASE architecture provides.
Westcon-Comstor to distribute Zscaler in UK&I, Germany, Switzerland and France
Why the Evolution of Zero Trust Must Begin with Data Protection
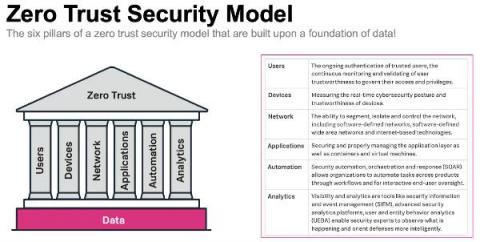
The need for “Zero Trust” today is no longer the same as what we talked about years ago when the term was first coined. Back then, businesses only had a handful of remote workers signing in to the corporate network. The common wisdom of the day dictated that you couldn’t implicitly trust the authentication of those remote users any longer because they weren’t on the company LAN and the common solution was installing two-factor authentication.
Why the New Executive Order will result in wider rollout of Zero Trust Adoption
A Zero Trust Security Approach for Government: Increasing Security but also Improving IT Decision Making
Public sector organisations are in the middle of a massive digital transformation. Technology advances like cloud, mobile, microservices and more are transforming the public sector to help them deliver services as efficiently as commercial businesses, meet growing mission-critical demands, and keep up with market expectations and be more agile.
Spectra Alliance Helps Enable Zero Trust
Zero Trust is not something you purchase. Zero Trust is a security strategy you build out using the working assumption that there are no safe network zones, no perimeters, no safe users, and no safe devices. The Spectra Alliance helps enable a Zero Trust model across the scope of six elements including applications, data, networks, infrastructure, identities, and devices.