Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Testing
London or Chicago? It Depends on Many Refactors
In this post we discuss two styles of Test Driven Development (TDD): Bottom Up (Chicago style) and Top Down (London style) also known as mockist style. We show how both styles can be used application development and how refactoring may affect the tests.
Defense in Depth: Why You Need DAST, SAST, SCA, and Pen Testing
When it comes to application security (AppSec), most experts recommend using Dynamic Application Security Testing (DAST) and Static Application Security Testing (SAST) as “complementary” approaches for robust AppSec. However, these experts rarely specify how to run them in a complementary fashion.
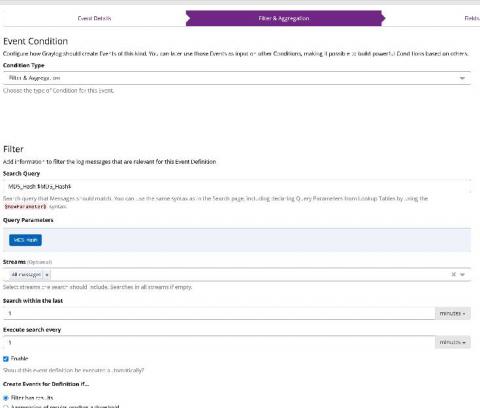
Red Team Tools Detection and Alerting
The FireEye breach on Dec 8, 2020, was executed by a “nation with top-tier offensive capabilities.” These hackers got a hold of FireEye’s own toolkit, which they can use to mount new attacks globally. What does this mean for you? Mandiant is a leading Red Team/Penetration Testing company with a highly sophisticated toolkit, called the "Red Team tools." These are digital tools that replicate some of the best hacking tools in the world.
How to build a serial port fuzzer with Defensics SDK
Defensics SDK makes fuzz testing possible for custom protocols. Learn how to create a custom injector using the Defensics SDK API. Fuzz testing is never a bad idea. If you aren’t testing your implementation with malformed or unexpected inputs, someone else may be able to exploit a weakness simply from running the system. And fuzz testing (or fuzzing) is not only about finding potential security issues—it can also increase the overall robustness of the system.
Build and Upload Files to Scan Using Veracode Static for Visual Studio
What You Need To Know About Application Security Testing Orchestration
As the security threat landscape continues to evolve, choosing the best application security testing tools is just the first challenge for organizations investing in AppSec. Next, organizations need to figure out how to best orchestrate the application security testing technologies they are using in order to get the most out of them without losing valuable time. That’s where application security testing orchestration comes in.