Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
ASM
Winning the battle against vulnerabilities with an EASM tool
The Complete Vulnerability Assessment Checklist
Navigating the Shift: From Vulnerability Management to Continuous Threat Exposure Management
In the rapidly evolving cybersecurity landscape, organizations face an ever-increasing barrage of threats. Traditional vulnerability management, while foundational, often falls short in proactively and continuously identifying and mitigating threats. This necessitates a paradigm shift towards Continuous Threat Exposure Management (CTEM), a more dynamic approach that aligns with the complexities of today’s digital environments.
Identifying Blind Spots Through External Attack Surface Management
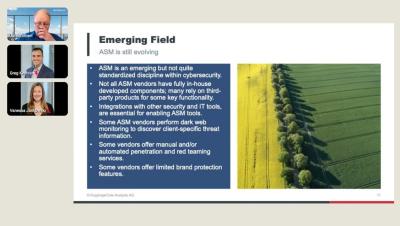
Unlock the Power of Attack Surface Management with Insights from a KuppingerCole Analyst
The Security Performance Management Evolution: Interview with Bitsight's Greg Kesen & Dark Reading
Critical Features Your Attack Surface Management Tool Must Have
Outpost24 Expands Leading External Attack Surface Management Solution with Credential Threat Intelligence
How to Reduce Your Attack Surface
An attack surface is the total number of channels, pathways, or areas that threat actors can utilize to gain unauthorized access to networks. The result is that they can obtain private information or carry out a cyber-attack. An attack surface comprises the organizational assets a threat actor can exploit to gain unauthorized access. Attack surfaces include systems that are directly involved in mission-critical operations, as well as those that provide peripheral services or access to important data.