Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Fraud
Unveiling INETCO Insight 7: The next generation of real time payment fraud detection and prevention
UK Card Fraud Accounts for Half of All Losses Across Europe
New findings from FICO claim that UK card fraud accounts for over half of all losses across Europe. The firm's new European Fraud Map reveals that UK card fraud losses hit over £671 in 2018, representing a 19% increase from the losses accumulated in 2017. UK card fraud losses amount to almost half of the £1.6 billion in total losses recorded across the 19 countries in the European interactive map, including Ukraine, Russia, and Turkey.
Winter Is Here, and so Are Holiday Cyber Scams
The holiday season revolves largely around traditions like festive lights, Christmas trees, family dinners, holiday cards and Secret Santa gift exchanges. Even if you don't like all of these traditions, you will probably agree that none is as bad as one of the newest phenomena that characterizes this time of year: holiday cyber scams.
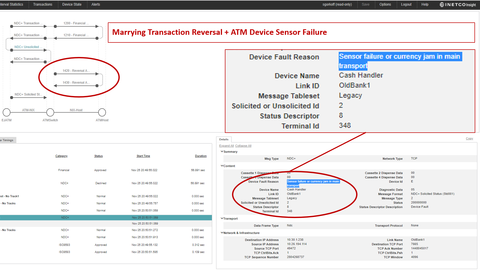
Security Update: Transaction Reversal Fraud - UK Edition
On November 21st, NCR issued a security alert for a new form of Transaction Reversal Fraud (TRF) occurring in the UK, typically between 10 PM and midnight on any given day. Contrary to previously reported TRF attacks in which cash is pried from the dispenser after a payment reversal is initiated due to the jamming of the card reader, this new method does not require any interaction with the card reader or the use of modified cards.
Top 3 Fraud Detection and Machine Learning Tips to Identify High-Risk Customer Banking
There are scary villains out there, and they don’t just come out on Halloween. Forget about tricks, and treat yourself to something worth reading…but be warned…this blog is not for the faint of heart… The authentication or the decline of a payment transaction is often the defining factor of end customer experience.
The Evolution of Phishing: The Spear Is Aimed at You
You can’t go a week without seeing a story about a data breach or ransomware hitting organizations. These breaches can be very costly, but they still continue to show up. Are the good guys not winning the cybersecurity war? Organizations invest millions of dollars in security products and services, but they keep getting breached.
Top Tax Scams to Watch out For
Diligent taxpayers are being increasingly targeted by con artists who are well-versed in manipulating the revenue system. The crooks usually impersonate IRS (U.S. Internal Revenue Service) officials, sending fake emails or messages on social media in an attempt to defraud the targeted individuals of their money. Unfortunately, lots of people fall for these scams, and the malefactors are raking in significant profits. Below is a list of the prevalent tax swindles doing the rounds nowadays.
What is Email Spoofing?
Email spoofing is the creation of emails with a forged sender address. Because core email protocols lack authentication, phishing attacks and spam emails can spoof the email header to mislead the recipient about the sender of the email. The goal of email spoofing is to get recipients to open, respond and engage with the email message. Email spoofing can greatly increase the effectiveness of phishing and other email-based cyber attacks by tricking the recipient into trusting the email and its sender.