How the MITRE ATT&CK Framework Helps CISOs Communicate Risk to Stakeholders
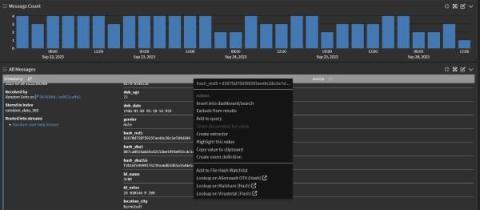
Picture this: Your CEO comes into your office and asks, “What’s our security posture, and where’s our greatest area of risk? I’m particularly worried about this new emerging threat group. What defenses or detections do we have around that?” You: “…” Enter the MITRE ATT&CK® framework and Devo’s MITRE ATT&CK Adviser app—built to help you tell the business where your risks are and what it would take to address them.