Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Security
One Year Later: First GDPR Execution Overview Reveals There's Still Work to Do
It’s been nearly a year since the European Union’s General Data Protection Regulation (GDPR) became enforceable. In that span of time, news outlets have reported various stories largely concerning the regulation and its penalties scheme.
The future of stock market analysis
Stock sales and trading play a huge role in the U.S. and global economy. Stock exchanges provide the backbone to the economic infrastructure of our nation, as they help companies to expand when they’re ready by offering the general public a chance to invest in company stock. However, investing in the stock market can be a gamble.
Internal Audit Checklist for Your Manufacturing Company
The manufacturing industry faces increasing scrutiny from regulatory agencies. As cybercriminals increasing target SCADA system weaknesses, an organization’s cybersecurity posture becomes more important to its ability to protect data and obtain important contracts. Starting with a security-first approach to cybersecurity often protects data, but to meet compliance requirements, the organization need to document the effectiveness of its internal controls.
Employee Investigations 101
Every visionary business wants to onboard the best of the best when it comes to talent. When hiring, companies look for hardworking, trustworthy individuals that they can rely on to propel the business forward. Similarly, people don’t typically hire people thinking they might start stealing money or misusing information and resources. Unfortunately, this happens quite regularly.
NNT ITSM Integration for Cherwell
Letting Go While Holding On: Managing Cyber Risk in Cloud Environments
As recently as 2017, security and compliance professionals at many of Tripwire’s large enterprise and government customers were talking about migration to the cloud as a possibility to be considered and cautiously explored in the coming years. Within a year, the tone had changed.
Adversary simulation with USM Anywhere
In our previous blog, we analyzed how it is possible to map malware threats using the MITRE ATT&CK™ framework. In this blog, we will test the USM Anywhere platform against red team techniques and adversary simulations. We performed this analysis as part of our continuous efforts to improve the platform’s detection effectiveness.
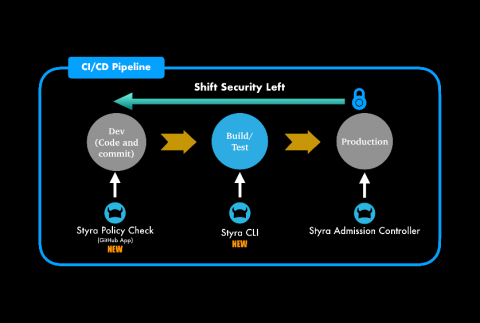
Enhancing Kubernetes Security by Shifting Security Left
In the rapidly evolving world of Kubernetes security & compliance, DevOps and DevSecOps teams are detecting security challenges and compliance issues later in the development & deployment cycles. We are excited to share new features and updates that help DevOps and DevSecOps teams detect issues and ensure compliance throughout the development cycle.
Things You Need to Know About Open Source - The FAQ Edition
Open Source projects can be a great asset, or they can be a curse – it’s all in how you manage it. To be successful in using open source, there are several things to keep in mind, from licensing to updates. And if you ignore any of them, it can cause problems. Here are some things to consider.