Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest Posts
Threat Actors Distributing Screenshotter Malware from OneDrive
Europe's Regulatory Environment to Drive Automation in GRC
Netskope Threat Labs Stats for December 2023
Netskope Real-time Threat Protection and AV-TEST Results
Netskope continues to advance inline threat protection capabilities and has improved its detection and blocking of malware and phishing attacks while also lowering and improving its false positive rate in the latest AV-TEST Report. In every part of the testing, Netskope improved.
Netskope GovCloud Receives FedRAMP High Impact Authorization
At Netskope, we have a long history of supporting customers in the US Federal Government. For example, the US Patent and Trademark Office (USPTO) recently chose Netskope to help with its cloud-first security initiatives, building out their entire SASE architecture. Today, we’re thrilled to announce two major developments to make it easier to acquire and implement Netskope in US federal agencies and the contractors that support them.
A Look at the Nim-based Campaign Using Microsoft Word Docs to Impersonate the Nepali Government
Threat actors often employ stealthy attack techniques to elude detection and stay under the defender’s radar. One way they do so is by using uncommon programming languages to develop malware. Using an uncommon programming language to develop malware provides several benefits, including: Netskope recently analyzed a malicious backdoor written in Nim, which is a relatively new programming language.
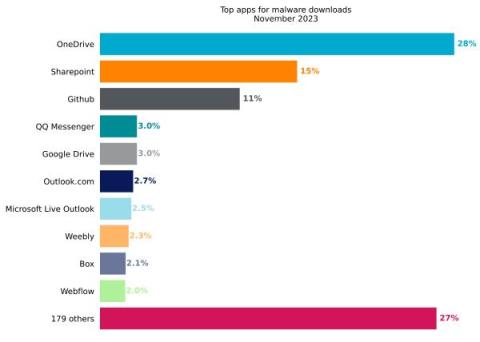
Netskope Threat Labs Stats for November 2023
Netskope Threat Labs publishes a monthly summary blog post of the top threats we are tracking on the Netskope platform. The purpose of this post is to provide strategic, actionable intelligence on active threats against enterprise users worldwide.
Cloud Threats Memo: Extracting Training Data from Generative AI Language Models
This year will probably be remembered for the revolution of ChatGPT (the website was visited by 1.7 billion users in October 2023, with 13.73% of growth compared to the previous month) and for the widespread adoption of generative AI technologies in our daily life.
The Winter Wonderland of Cyber Threats
It’s the season for mince pies, tinsel and, of course, holiday shopping. I am in the Middle East so temperatures are quite pleasant for a mall stroll while shopping for family gifts, but it’s certainly odd hearing Mariah Carey being played and seeing fake snow on Christmas trees when it’s 25 degrees outside. While I prefer to do my shopping in person, around the world the majority of festive shopping happens on mobiles and laptops.