Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
DevSecOps
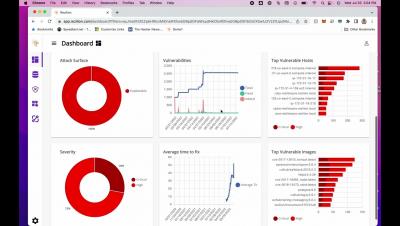
Reduce Your Software Attack Surface with Rezilion
Data Flow Mapping: Why It Matters and How to Do It
Working with data is something that requires a lot of care and precision, yet it often remains an under-scrutinized aspect of DevSecOps. This is because it requires focusing on many moving parts. You need to know exactly when data events occur, what parties are involved, and how they send and store data. In any process with more than minimal complexity, this is a huge web of events. Data flow mapping is the key to detangling that web.
Snyk Unveils Snyk Cloud, the Industry's First Developer-Centric Cloud Security Solution
CrowdStrike Expands CNAPP Capabilities to Secure Containers and Help Developers Rapidly Identify and Remediate Cloud Vulnerabilities
Wet signatures cost more than you might think
Speaking to people on our neighbouring booths at the UK nuclear decommissioning event, it was clear to see the entire industry is drowning in paperwork.
5 Essential Skills to Become a DevSecOps Engineer
Security has become increasingly integrated with software development over the last few years, and the software industry needed a new role to own secure software development processes. As a result, DevSecOps Engineer role has emerged and gained popularity in the last decade. DevSecOps is the abbreviation of three words; Development, security, and operations, and it aims to develop applications more securely in the software development life cycle (SDLC).
Webinar recap: Snyk and the new era of software security
Snyk’s Senior Product Marketing Manager, Frank Fischer, recently hosted a webinar about the value in using a developer security platform to secure code, dependencies, containers, and infrastructure as code (IaC). During this talk, Fischer discussed the shift in software security that has occurred over the past decade, the need for developers to take part in the security process, and the value of Snyk in securing the entire development lifecycle.
How To Put Cloud Nimble to Work to Shift Left Security
Shifting security left means preventing developers from using unacceptably vulnerable software supply chain components as early as possible: before their first build. By helping assure that no build is ever created using packages with known vulnerabilities, this saves substantial remediation costs in advance. Some JFrog customers restrict the use of open source software (OSS) packages to only those that have been screened and approved by their security team.