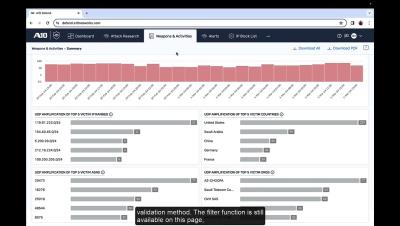
Demo: A10 Defend Threat Control
A10 Defend Threat Control provides a robust first layer of DDoS defense. By leveraging proprietary ML/AL-enhanced data processing techniques, Threat Control proactively monitors attackers and understands key DDoS attack methods, with or without dedicated DDoS prevention solutions.