How to Enhance Your Network Security Strategy
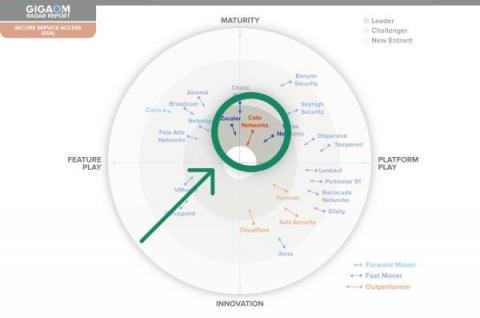
With the transition to the cloud and remote work, some organizations are undervaluing network security. However, network vulnerabilities and threats still require attention. Enterprises should not forgo the core capabilities required to secure the network from security threats. In this blog post, we delve into SASE, a converged, cloud-delivered network and security solution, which protects the network while ensuring high performing connectivity.