Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
January 2023
WhiteHat Dynamic Application Security Testing (DAST) | Synopsys
How to Test a Java Application
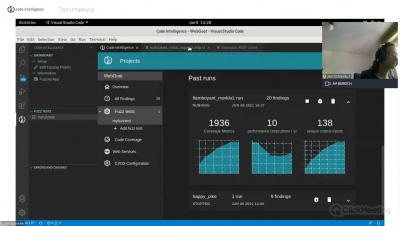
Why do we need a new approach to SAST?
Many companies provide legacy static application security testing (SAST) tools or engines, but their usefulness has not kept pace with the needs of an application-driven world. In order to succeed, businesses need a modern approach to SAST that will greatly improve it’s value in the software development lifecycle. In this blog, I look at the problems with traditional SAST tools, why there needs to be a change of approach in the SAST market, and what the future holds for SAST.
7 Challenges of Embedded Software Security Testing in 2023
We live in a world that depends on embedded software. It’s in the cars we drive, the elevators we take and the airplanes we travel in. As these systems become more and more complex, it becomes increasingly challenging to ensure that the interaction between embedded software and hardware remains functional and secure. Due to the nature of embedded systems and the devastating consequences of failures, many traditional testing methods fall short of providing adequate security for them.